标题: [注册表类] 批处理借助工具SecEdit更改注册表子项所有者不成功,帮忙看看错在哪?谢谢! [打印本页]
作者: Shuye 时间: 2023-2-14 19:27 标题: 批处理借助工具SecEdit更改注册表子项所有者不成功,帮忙看看错在哪?谢谢!
子项HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Classes\CLSID\{679f85cb-0220-4080-b29b-5540cc05aab6}\ShellFolder
想将其所有者 SYSTEM 更改为 ADMINISTRATORS
打开注册表,手动可以改,但借助工具 SecEdit 却不成功。- Pushd "%Temp%"
- > SecFile.inf (
- Echo [Version]
- Echo Signature="$CHICAGO$"
- Echo [Registry Keys]
- Echo "MACHINE\SOFTWARE\WOW6432Node\Classes\CLSID\{679f85cb-0220-4080-b29b-5540cc05aab6}\ShellFolder", 0, "O:BA"
- )
- SecEdit /Configure /db SecFile.sdb /Cfg SecFile.inf /Log SecFile.log
- Popd
老师帮忙看看错在哪?谢谢啦!
作者: 1073 时间: 2023-2-14 20:13
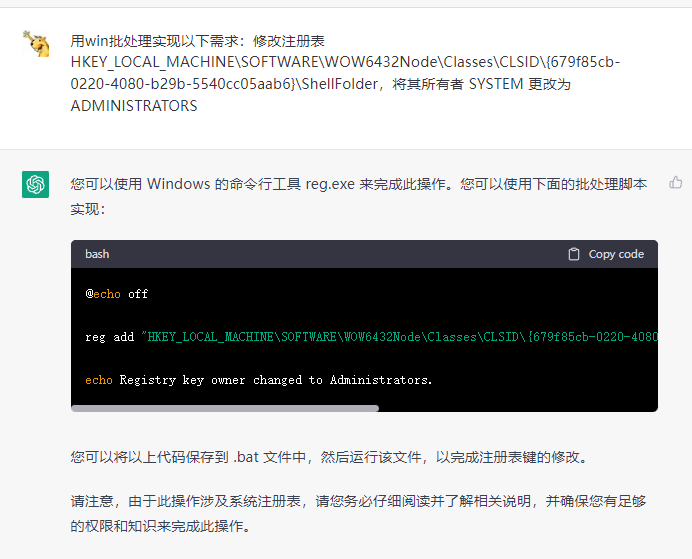
帮你问了一下chatGPT,不知道对不对啊
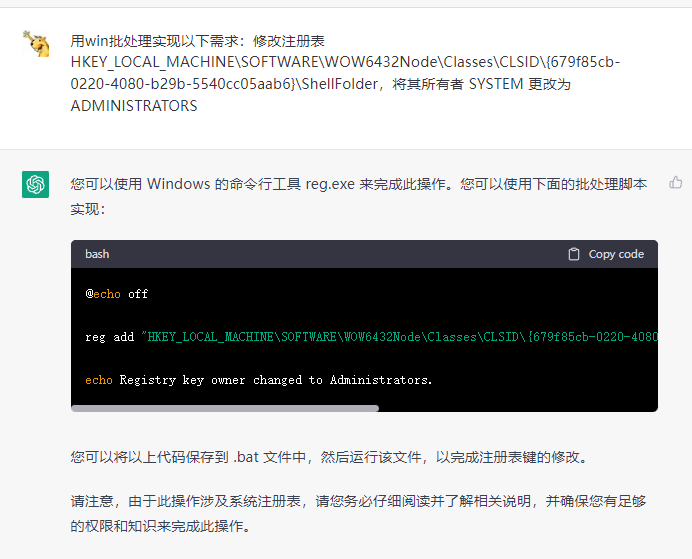
- @echo off
-
- reg add "HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Classes\CLSID\{679f85cb-0220-4080-b29b-5540cc05aab6}\ShellFolder" /v Owner /t REG_SZ /d "Administrators" /f
-
- echo Registry key owner changed to Administrators.
作者: czjt1234 时间: 2023-2-14 20:17
chatGPT
作者: Shuye 时间: 2023-2-15 00:06
回复 2# 1073
谢谢 1073 兄!不过,还是不成功。
虽然执行后结果显示:操作成功完成。
但是,该项的所有者依旧还是“SYSTEM”,只是添加了一项键值:"Owner"="Administrators"
作者: Shuye 时间: 2023-2-15 01:21
本帖最后由 Shuye 于 2023-2-15 01:23 编辑
奇怪的是,有些子项用 SecEdit 是可以更改的,
如:MACHINE\SYSTEM\CurrentControlSet\Services\DPS ,用 SecEdit 改来改去都行。
偏偏就 MACHINE\SOFTWARE\WOW6432Node\Classes\CLSID\{679f85cb-0220-4080-b29b-5540cc05aab6}\ShellFolder 不行,
虽然执行后结果显示:任务成功结束,但实际上,注册表并没有更改。
作者: czjt1234 时间: 2023-2-15 09:30
会不会是需要管理员权限?
作者: Batcher 时间: 2023-2-15 11:31
回复 2# 1073
肯定是错误,它根本没有理解需要实现什么功能。
作者: WHY 时间: 2023-2-15 13:07
- @echo off
- REM 右键以管理员身份运行
- cd /d "%~dp0"
- set "regPath=HKLM\SOFTWARE\WOW6432Node\Classes\CLSID\{679f85cb-0220-4080-b29b-5540cc05aab6}\ShellFolder"
- SetACL -on "%regPath%" -ot reg -actn setowner -ownr "n:Administrators" -actn rstchldrn -rst dacl
- pause
我测试没有问题
SetACL3.1.2 下载地址:https://helgeklein.com/downloads ... utable version).zip
作者: 1073 时间: 2023-2-15 13:53
回复 7# Batcher
应该还是需求表述的不到位
作者: Shuye 时间: 2023-2-16 01:26
回复 8# WHY
测试成功,效果很好,谢谢 WHY 兄!
还想问问:除此之外,不借助第三方工具能不能达到这效果 ?
作者: WHY 时间: 2023-2-16 16:42
还想问问:除此之外,不借助第三方工具能不能达到这效果 ?
PowerShell,可以将 SYSTEM 所有者更改为 Administrators;反之则不行(SYSTEM账户权限高于Administrator,要调用winAPI)- <# :
- @echo off
- REM 右键以管理员身份运行
- set "regPath=HKLM\SOFTWARE\WOW6432Node\Classes\CLSID\{679f85cb-0220-4080-b29b-5540cc05aab6}\ShellFolder"
- PowerShell -C ". ([ScriptBlock]::Create((gc -Literal '%~f0') -join \"`r`n\")) '%regPath%'"
- pause & exit
- #>
-
- param([string]$regPath);
-
- Switch -regex ($regPath) {
- '^(?:HKLM|HKEY_LOCAL_MACHINE)' { $root = 'LocalMachine' }
- '^(?:HKCU|HKEY_CURRENT_USER)' { $root = 'CurrentUser' }
- '^(?:HKCR|HKEY_CLASSES_ROOT)' { $root = 'ClassesRoot' }
- '^(?:HKCC|HKEY_CURRENT_CONFIG)'{ $root = 'CurrentConfig' }
- '^(?:HKU|HKEY_USERS)' { $root = 'Users' }
- }
-
- $subKey = $regPath.Split('\', 2)[1];
- $objKey = [Microsoft.Win32.Registry]::$root.OpenSubKey($subKey, 'ReadWriteSubTree', 'TakeOwnership');
- $acl = $objKey.GetAccessControl();
- $acl.SetOwner([Security.Principal.NTAccount]'Administrators');
- $objKey.SetAccessControl($acl);
作者: WHY 时间: 2023-2-16 21:18
本帖最后由 WHY 于 2023-2-18 23:14 编辑
参考:https://www.likecs.com/ask-1396155.html
第4行是需要修改的注册表项路径,第5行是修改以后的所有者名称。
如果不需要连同子项一起修改,删除最后一行 Get-SubKeys $subKey;
2023/02/18 修复Win7(PowerShell v2.0)报错- <# :
- @echo off
- REM 右键以管理员身份运行
- set "regPath=HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Classes\CLSID\{FE38753A-44A3-11D1-B5B7-0000C09000C4}"
- set "OwnerName=NT SERVICE\TrustedInstaller"
- REM set "OwnerName=Administrators"
- PowerShell ". ([ScriptBlock]::Create((gc -Literal '%~f0') -join \"`r`n\")) '%regPath%' '%OwnerName%'"
- pause & exit
- #>
-
- param([string]$regPath, [Security.Principal.NTAccount]$owner);
-
- $Code = @'
- using System;
- using System.Security.Principal;
- using System.ComponentModel;
- using System.Runtime.InteropServices;
- namespace WinAPI{
- public static class Program{
- public static bool ModifyPrivilege(PrivilegeName privilege, bool enable){
- LUID luid;
- if (!LookupPrivilegeValue(null, privilege.ToString(), out luid)){
- throw new Win32Exception();
- }
- using (WindowsIdentity identity = WindowsIdentity.GetCurrent(TokenAccessLevels.AdjustPrivileges|TokenAccessLevels.Query)){
- TOKEN_PRIVILEGES newPriv;
- newPriv.Privileges = new LUID_AND_ATTRIBUTES[1];
- newPriv.PrivilegeCount = 1;
- newPriv.Privileges[0].Luid = luid;
- newPriv.Privileges[0].Attributes = enable ? SE_PRIVILEGE_ENABLED : 0;
-
- TOKEN_PRIVILEGES prevPriv;
- prevPriv.Privileges = new LUID_AND_ATTRIBUTES[1];
- prevPriv.PrivilegeCount = 1;
- uint returnedBytes;
-
- if (!AdjustTokenPrivileges(identity.Token, false, ref newPriv, (uint) Marshal.SizeOf(prevPriv), ref prevPriv, out returnedBytes)){
- throw new Win32Exception();
- }
- return prevPriv.PrivilegeCount == 0 ? enable : ((prevPriv.Privileges[0].Attributes & SE_PRIVILEGE_ENABLED) != 0);
- }
- }
-
- const uint SE_PRIVILEGE_ENABLED = 2;
-
- [DllImport("advapi32.dll", SetLastError = true)]
- [return: MarshalAs(UnmanagedType.Bool)]
- static extern bool AdjustTokenPrivileges(IntPtr TokenHandle, [MarshalAs(UnmanagedType.Bool)] bool DisableAllPrivileges, ref TOKEN_PRIVILEGES NewState, UInt32 BufferLengthInBytes, ref TOKEN_PRIVILEGES PreviousState, out UInt32 ReturnLengthInBytes);
-
- [DllImport("advapi32.dll", SetLastError = true, CharSet = CharSet.Auto)]
- [return: MarshalAs(UnmanagedType.Bool)]
- static extern bool LookupPrivilegeValue(string lpSystemName, string lpName, out LUID lpLuid);
-
- struct TOKEN_PRIVILEGES {
- public UInt32 PrivilegeCount;
- [MarshalAs(UnmanagedType.ByValArray, SizeConst = 1 /*ANYSIZE_ARRAY*/)]
- public LUID_AND_ATTRIBUTES[] Privileges;
- }
-
- [StructLayout(LayoutKind.Sequential)]
- struct LUID_AND_ATTRIBUTES {
- public LUID Luid;
- public UInt32 Attributes;
- }
-
- [StructLayout(LayoutKind.Sequential)]
- struct LUID {
- public uint LowPart;
- public int HighPart;
- }
- }
-
- public enum PrivilegeName {
- SeAssignPrimaryTokenPrivilege,
- SeAuditPrivilege,
- SeBackupPrivilege,
- SeChangeNotifyPrivilege,
- SeCreateGlobalPrivilege,
- SeCreatePagefilePrivilege,
- SeCreatePermanentPrivilege,
- SeCreateSymbolicLinkPrivilege,
- SeCreateTokenPrivilege,
- SeDebugPrivilege,
- SeEnableDelegationPrivilege,
- SeImpersonatePrivilege,
- SeIncreaseBasePriorityPrivilege,
- SeIncreaseQuotaPrivilege,
- SeIncreaseWorkingSetPrivilege,
- SeLoadDriverPrivilege,
- SeLockMemoryPrivilege,
- SeMachineAccountPrivilege,
- SeManageVolumePrivilege,
- SeProfileSingleProcessPrivilege,
- SeRelabelPrivilege,
- SeRemoteShutdownPrivilege,
- SeRestorePrivilege,
- SeSecurityPrivilege,
- SeShutdownPrivilege,
- SeSyncAgentPrivilege,
- SeSystemEnvironmentPrivilege,
- SeSystemProfilePrivilege,
- SeSystemtimePrivilege,
- SeTakeOwnershipPrivilege,
- SeTcbPrivilege,
- SeTimeZonePrivilege,
- SeTrustedCredManAccessPrivilege,
- SeUndockPrivilege,
- SeUnsolicitedInputPrivilege,
- }
- }
- '@
-
- Add-Type -TypeDefinition $Code;
- [WinAPI.Program]::ModifyPrivilege('SeRestorePrivilege', $true);
- [WinAPI.Program]::ModifyPrivilege('SeTakeOwnershipPrivilege', $true);
-
- Switch -regex ($regPath) {
- '^(?:HKLM|HKEY_LOCAL_MACHINE)' { $root = 'LocalMachine' }
- '^(?:HKCU|HKEY_CURRENT_USER)' { $root = 'CurrentUser' }
- '^(?:HKCR|HKEY_CLASSES_ROOT)' { $root = 'ClassesRoot' }
- '^(?:HKCC|HKEY_CURRENT_CONFIG)'{ $root = 'CurrentConfig' }
- '^(?:HKU|HKEY_USERS)' { $root = 'Users' }
- }
- $subKey = $regPath.Split('\', 2)[1];
-
- Function Set-Owner($subKey){
- $objKey = [Microsoft.Win32.Registry]::$root.OpenSubKey($subKey,'ReadWriteSubTree', 'TakeOwnership');
- $acl = $objKey.GetAccessControl();
- $acl.SetOwner($owner);
- $objKey.SetAccessControl($acl);
- $objKey.Close();
- }
-
- Function Get-SubKeys($subKey){
- $objKey = [Microsoft.Win32.Registry]::$root.OpenSubKey($subKey);
- $arrName = $objKey.GetSubKeyNames();
- $objKey.Close();
- forEach( $subName In $arrName ){
- Set-Owner ($subKey + '\' + $subName);
- Get-SubKeys ($subKey + '\' + $subName);
- }
- }
-
- Set-Owner $subKey;
- Get-SubKeys $subKey;
作者: Shuye 时间: 2023-2-17 02:51
回复 12# WHY
先收藏,慢慢学习。非常感谢 WHY 兄!
| 欢迎光临 批处理之家 (http://www.bathome.net/) |
Powered by Discuz! 7.2 |